Cyber Security for the Internet of Things

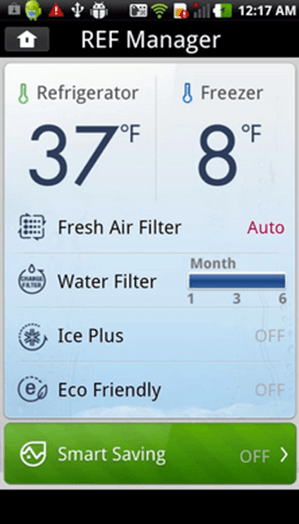 Every day, most people utilize Internet-connected devices like smartphones and mobile tablets. They may also use smart devices in their homes including Internet-connected televisions, thermostats and home security systems. In fact, connected devices can be as small as a mobile glucose monitor and as large as an Internet-connected automobile. Over the past few years, even home appliances like refrigerators have started to develop Internet functionality. For example, a homeowner can control the temperature inside of an Internet-connected smart refrigerator from any location by using a mobile app.
Every day, most people utilize Internet-connected devices like smartphones and mobile tablets. They may also use smart devices in their homes including Internet-connected televisions, thermostats and home security systems. In fact, connected devices can be as small as a mobile glucose monitor and as large as an Internet-connected automobile. Over the past few years, even home appliances like refrigerators have started to develop Internet functionality. For example, a homeowner can control the temperature inside of an Internet-connected smart refrigerator from any location by using a mobile app.
As a connected ecosystem, experts refer to these devices as the “Internet of Things” (IoT). Although the IoT offer many benefits, it also presents new and worrisome security risks. Between Dec. 23, 2013, and Jan. 6, 2014, the security firm Proofpoint discovered that attackers had used over 100,000 connected devices, from multi-media centers to TVs, from routers to refrigerators, to send around 750,000 malicious e-mails. Many security experts had theorized that IoT devices could be hacked, but Proofpoint’s analysis proved that the worst could actually happen. For this reason, security firms, device manufacturers, business owners and homeowners need to make sure that their current comprehensive cyber security and threat detection solutions providers have plans to protect their connected devices.
What Are Smart Appliances?
Electricity costs more at peak usage times of day. For example, running a dryer at 1 p.m. costs more than running a dryer at 9 p.m. because fewer people use electricity at night. With the smart grid, a utility company could control a connected appliance. For example, the utility company could delay a refrigerator’s defrost cycle until an off-peak time so that the electricity costs less. Alternatively, if a homeowner wanted to run a dryer during peak hours, a smart dryer could reduce the amount of wattage that its heating coils used to conserve power.
Smart appliances would also have the ability to learn. For instance, a break room refrigerator could track the typical times of day that an employee opens the door. After finding a pattern, the refrigerator could adjust its cooling periods to maximize energy efficiency. An oven could sense when a roast is done and could send a text message to the cook. By communicating with each other, home appliances could optimize their performance to minimize electricity costs. The possibilities for convenience and energy savings are tremendous, but smart appliances also provide a new front in cyber warfare.
Why Security Is a Problem
Smart devices are connected to the Internet. In many cases, they’re either set up incorrectly, or they utilize default passwords that attackers can easily find on public networks. In 2009, the global population was using about 2.5 billion connected devices. By 2020, Gartner predicts that the world’s population will use as many as 30 billion smart devices.
After compromising a device, attackers can set up the device to act as a botnet. A botnet is a zombie computer controlled by a hacker that can attack other computers. For example, a zombie device can bombard a website with traffic requests. Alternatively, botnets can, as they did in the Proofpoint case, send out hundreds of thousands of spam e-mails. When combined with huge numbers of zombie machines, botnets can disable major websites and critical infrastructure, like the electrical grid. Experts worry that attackers will move beyond laptops and desktop computers and focus their efforts on compromising connected devices.
Protecting the Internet of Things
Smart devices aren’t going anywhere. Just a few weeks ago, Google shelled out $3.2 billion to buy Nest, an obscure company that makes smart thermostats and smoke alarms. With big companies eyeing the IoT for big profits, security needs to make big strides to catch up with convenience.
IoT security solutions include limiting the communication ranges of smart devices. For example, smart devices within a building could communicate with each other, but they couldn’t communicate with the Internet at large. Some manufacturers encrypt the data that travels from a smart device to a smartphone app, and some stakeholders are developing software that will control access to smart devices according to job authority or other factors.
At the very least, a home or business with smart appliances needs a network security solution. Without cyber security, no one may notice the smart coffeemaker doing double duty as both an automated barista and a botnet.





I really like your blog.. very nice colors & theme. Did you design this website yourself
or did you hire someone to do it for you? Plz respond as I’m looking to design my own blog
and would like to find out where u got this from.
thanks