Want to play your friend’s Steam games? Here’s how to use Steam Family Sharing
Steam is the most popular digital distribution platform for PC games, and if you are into PC gaming, it’s likely you and your friends have built up a substantial library of Steam games over the years. Although the service has frequent sales, one can only afford to buy so many games. Thankfully, if one of your friends owns a game that you don’t, it is possible for you to play it — without borrowing their computer — thanks to Steam’s Family Sharing function. The process is simple, and allows you to share your library with up to five other accounts, so if your friend wants to try, say, Shadow of Mordor from your account, they can do so hassle-free. Here’s how it works.
More: Kick off your streaming career with our complete guide to Twitch broadcasting
Before you share your account, you must enable the “Steam Guard” feature, which requires you to input a code — received by email or text message — when someone logs into your Steam account from a new computer.
To activate Steam Guard, log into your account and open Preferences.
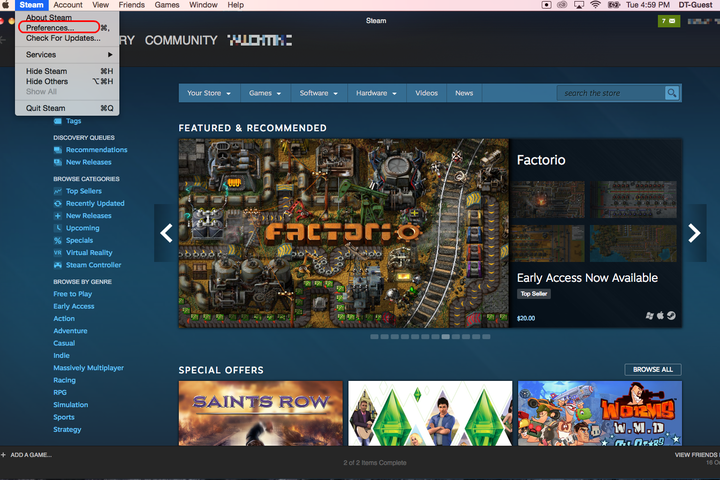
In the Account tab, click the button labeled Manage Steam Guard Account Security…
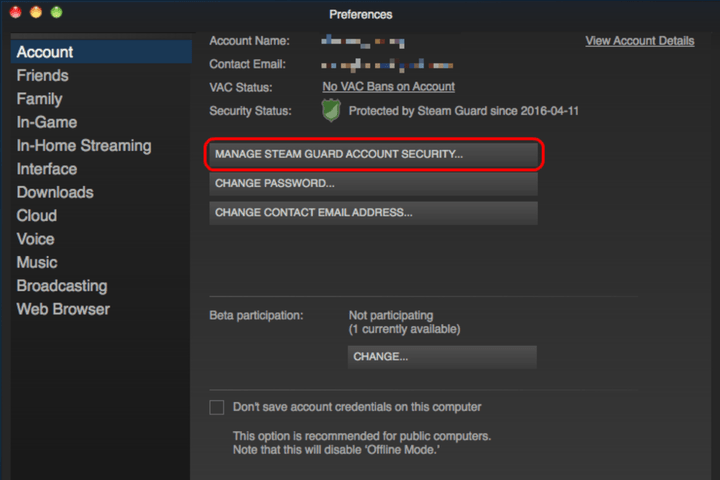
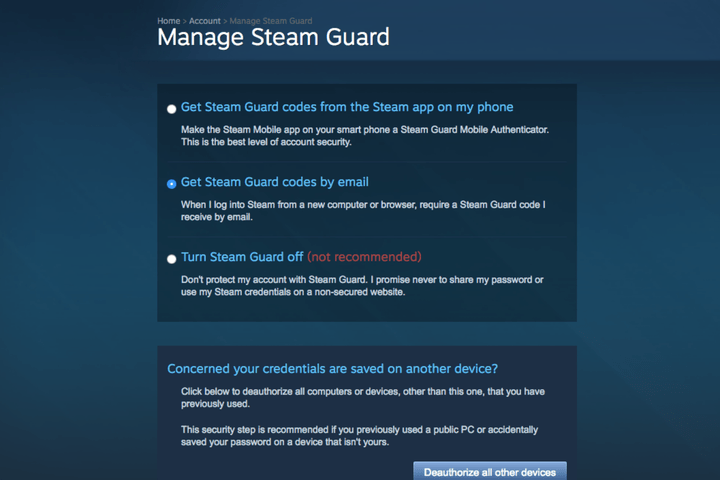
Next, select whether you want to receive your Steam Guard notifications via text or email.
With Steam Guard activated, you will be able to share your library with another computer. To do so, you must log into your Steam account on that computer and go to your Preferences. Afterward, select the tab labeled Family.

Check the box labeled Authorize Library Sharing on this computer.
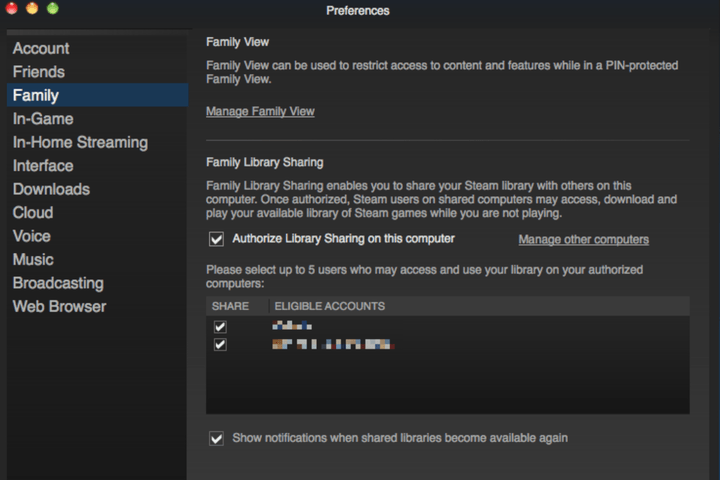
You should see a list of accounts that have also logged into that computer in the past. Check whichever ones you want to share with, then click the box labeled OK. Now, when your friend logs into the selected account on that computer, they will be able to download and play games from your library.
Keep in mind, however, that there are limits to Family Sharing: Two users cannot access the same library at the same time. In the event that you and your friend both want to play a game from the same account at the same time, the library’s owner gets priority.
Twitter user finds how much info you can glean from a locked phone
Why it matters to you
Think a locked iPhone is safe from prying eyes and ears? Think again. You’ll want to change your settings after reading what this Twitter user discovered.
If physical locks can be picked, it stands to reason that our digital locks can be broken, too. And sometimes, it doesn’t even take a mastermind hacker to access information protected by a password. In fact, iPhone owners may be horrified to find out that their trusty personal assistant is giving them up. That’s right — Siri, whom you’ve always trusted to help you out in a tight spot, may not be as loyal as you think.
A Twitter user recently discovered that even a locked iPhone can reveal many of your secrets — or at least quite a bit of your personal information. As @afronomics_ explained in a series of tweets, after she found a locked iPhone in a bathroom and tried to return it to its rightful owner, she found out just how much Siri was willing to divulge when it comes to her owner’s data.
More: With the SiriusXM Onyx Plus, you won’t be left struggling with FM radio ($64)
“I asked siri what’s my name,” @afronomics_ tweeted, “It pulled up her info. Cool. I asked Siri who do I call most. Pulled up her recent calls. Cool.” More like yikes.
it was that easy. all from a locked phone. I could've got directions to her car and her home. that shit scared me.
— uninterested hō (@afronomics_) February 20, 2017
And that’s not the only information Siri was willing to give up. The Twitter user was able to find her recent call log, her notifications, her first and last name, where she lived, and the location of her car. “It was that easy,” @afronomics_ wrote, noting that she could’ve asked for directions to the iPhone owner’s car and home. Truly a frightening thought.
I told the girl. she was shook. then I changed her settings for her so that couldn't happen.
— uninterested hō (@afronomics_) February 20, 2017
But don’t worry, friends. Not only was the iPhone returned to its rightful owner, but the finder also gave her a few tips on how to ensure that Siri wouldn’t be so loose-lipped. All you have to do is head over to Settings, navigate to Touch ID & Passcode, then under “Allow Access When Locked,” turn off Siri, Today’s View, and Notification View. Because you have enough to worry about on a daily basis without worrying about what Siri is telling strangers about you.
ZeniMax files for injunction that could bar Oculus from selling VR headsets
Why it matters to you
ZeniMax’s legal action against Oculus VR could have a profound impact on the contest for supremacy in the virtual reality headset space.
Earlier this month, ZeniMax’s legal battle with Oculus VR closed out its first chapter when a court found that members of the Facebook-owned virtual reality company had failed to comply with non-disclosure agreements. ZeniMax was awarded $500 million in damages, but the video game publisher has now taken steps to reignite its dispute with Oculus.
On Thursday, ZeniMax representatives appeared in a federal court in Dallas, Texas to request an injunction against Oculus. If successful, the company will be blocked from using the code at the center of the earlier court case — it’s alleged to be based on work carried out by John Carmack before he jumped ship from ZeniMax subsidiary Id Software.
This injunction could have a huge impact on Oculus if it is granted, perhaps even more so than the damages the company was ordered to pay on February 1. It could prevent devices including the Oculus Rift and Samsung Gear VR from being sold, as well as potentially taking some VR games off the market, according to a report from Tom’s Hardware.
More: Oculus Rift still facing issues with room-scale tracking, but a fix is on the way
The code in question is thought to be used in Oculus’ hardware, and is also said to have been distributed to certain developers for use in their projects. If this is the case, those products might themselves have to be pulled from sale.
However, it’s not yet clear whether or not ZeniMax’s injunction will be successful. While Oculus staff were found to have breached non-disclosure agreements earlier this month, the court ruled that the company had not misappropriated trade secrets.
Shortly after the case was decided, Carmack weighed in with his thoughts on ZeniMax’s claims of code theft, criticizing some of the arguments leveled against him, and the plaintiff’s expert in particular. “The notion of non-literal copying is probably delicious to many lawyers, since a sufficient application of abstraction and filtering can show that just about everything is related,” he wrote, going on to downplay the concrete similarities between work he submitted to Id Software and Oculus’ code.
The quarrel between ZeniMax and Oculus seems poised to run on and on, and if successful, this injunction could have a major impact on the VR landscape. $500 million in damages isn’t a huge setback for a company backed by the deep pockets of Facebook — being forced to withdraw Rift hardware from sale, on the other hand, would be a major obstacle to overcome.
The FAA has yet to confirm any drone-airplane collisions, despite more sightings
Why it matters to you
Many are concerned about the possibility of a drone colliding with a passenger aircraft, but the FAA hasn’t confirmed a single incident.
The latest Federal Aviation Administration reports show a growth in the number of pilots reporting potential encounters with drones but the organization has yet to confirm any of the unmanned aerial vehicles hitting an aircraft in the U.S.
The report, released on Thursday, details possible drone sightings from February through September 2016. The FAA identified 1,274 potential sightings, while the same time frame the previous year only produced 874 reports.
More: More drone crashes caused by technical glitches, not human error, study shows
“Although the data contain several reports of pilots claiming drone strikes on their aircraft, to date the FAA has not verified any collision between a civil aircraft and a civil drone,” the FAA wrote in an updated release. “Every investigation has found the reported collisions were either birds, impact with other items such as wires and posts, or structural failure not related to colliding with an unmanned aircraft.”
Operating drones near airports, airplanes, and helicopters is illegal and could lead to fines and jail time. The FAA uses a B4UFLY app to help hobbyist pilots determine where it’s safe to fly, while commercial drone pilots need to pass a test that includes understanding maps showing where flights are restricted.
While consumer drone sales doubled in 2016 at the same time the number of potential drone collisions was reported, the FAA says the reports contain a number of collisions with birds and other objects unrelated to drone flight. Every potential drone sighting near an aircraft, whether reported by pilots, law enforcement or civilians, is investigated, the FAA says.
“Reputable analyses of FAA data show that many ‘possible drone sightings’ turn out to be perfectly legitimate drone flights, or objects that clearly are not drones, and we expect these latest reports will show the same pattern,” said Kara Calvert, the Executive Director of the Drone Manufacturers Alliance. “The Drone Manufacturers Alliance expects all our members’ customers to fly safely, responsibly and far away from airplanes and helicopters. That’s why our members are constantly developing new technology to enhance safety, while working closely with the FAA and promoting its Know Before You Fly campaign to encourage educated flight.”
Google outage causes confusion, as devices log out and reset to factory defaults
Why it matters to you
If you have a Google Account, you might have experienced some weird login issues last night, but it doesn’t look like the outage compromised your security.
Late last night, Google experienced a bizarre outage which caused a number of devices to misbehave. The devices in question, the OnHub router, Google Wifi, and Chromecast, all logged themselves out of their user accounts, and in some cases went so far as to reset themselves to factory settings.
It’s unknown precisely how many devices were affected, but it appears to be the result of an internal issue at Google, not some kind of malicious attack. According to Tech Hive, if you were logged out of your device last night, your data is secure, but you might have to set up the device all over again.
We know some of you had issues signing in today. Please try again now. Rest easy — your account's security was not affected.
— Google (@Google) February 24, 2017
The Google Wifi mesh network routers, and the last-gen Google OnHub routers were the most profoundly affected by the outage. Instead of just being logged out, the Google routers were reset to factory defaults. If your router was affected, you’ll have to set up your network all over again.
“We experienced an issue with our Google Accounts engine that may have affected your Google Wifi or OnHub device. This causes some devices to automatically reset to the initial state you bought them in,” reads the Google help page dedicated to the issue.
Google’s Accounts Engine, the beating heart of your Google experience, appears to have been the culprit. While it’s certainly convenient to login to so many devices and services with the same account, last night’s outage illustrates one of the dangers posed by convenience. When one account goes down, all the services and devices reliant upon it will follow suit — like dominoes.
More: Google’s Gboard keyboard on iOS adds new languages, voice typing, and more
Luckily, last night’s outage was over quickly, and doesn’t appear to have been too widespread. Being logged out and having a few devices reset to factory settings is inconvenient, but not dangerous.
Still, while you’re rebuilding your home network, and logging into your Google accounts again, now would be a good time to make sure you have two-factor authentication enabled, and change your passwords just for good measure.
Protect files and apps on your Galaxy S7 with Samsung’s Secure Folder
Why it matters to you
Samsung’s Secure Folder makes encrypting sensitive content on your smartphone easier than ever, and adds critical features for locking apps and accounts behind an added layer of security.
We store our entire lives on our smartphones, and at one point or another, every user has sensitive content on their device they’d rather keep private from prying eyes. That’s surprisingly hard to do on Android or iOS without a third-party app, as neither platform gives users the ability to create encrypted storage spaces out of the box. Fortunately, Samsung is bucking that trend by launching Secure Folder support for its Galaxy S7 and S7 Edge smartphones.
Secure Folders actually debuted on last year’s Galaxy Note 7, though, regrettably, not many owners got the chance to become well-acquainted with the feature. That’s changing now that Samsung has released a downloadable version through its Galaxy Apps store. Secure Folders pretty much accomplish exactly what you’d imagine they would, allowing users to lock images, documents, and even apps behind a form of authentication, be it a PIN, password, pattern, or fingerprint.
More: Samsung Galaxy S8 rumors and news leaks

Samsung
What differentiates Secure Folder from other solutions, however, is that it can actually be used to store copies of apps with their own unique data, sandboxed from the rest of the phone. For example, a user could copy Twitter to a Secure Folder, and use that copy of the app for a separate account that wouldn’t be accessible from the original app on the home screen. As Samsung notes in its Newsroom post, “any notes, photos, contacts or browsing history within the apps stored in Secure Folder will remain separate from the same apps outside Secure Folder.”
That is a useful, powerful addition that is sure to please users managing high-risk information on their phones every day, made better by the fact that Secure Folders also support Samsung’s cloud-based backup and restore functionality. These backups remain isolated from the phone’s other general backup files, and are tied to a single Samsung account.
Finally, Samsung points out that Secure Folders can be customized with different names and icons to make them less conspicuous, or be hidden from the Apps screen entirely. Secure Folder is currently only compatible with Galaxy S7 devices running Android 7.0, though Samsung says it expects to bring the app to more of its phones in the future.
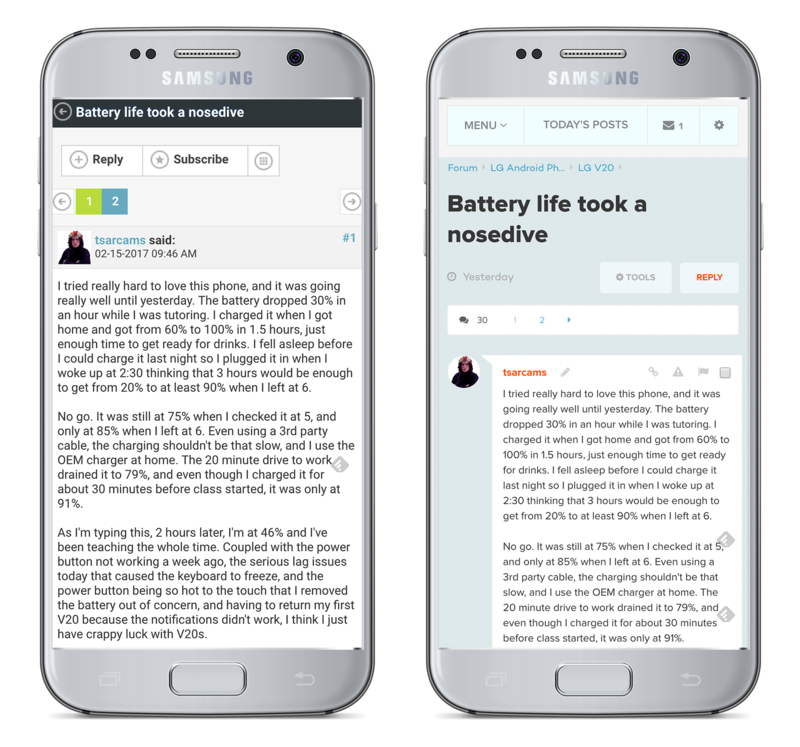
Our new forums are here!
We’ve redesigned our Forums to make them more accessible to more users — all while maintaining what made them great for our seasoned community members to start!

We want more people reading and engaging with the great content that is being produced in our Forums. Here is an overview of some of the biggest changes – a big thank you to Gio Martinez in particular for absolutely crushing it in coding these new designs, and to our community for helping us with feedback throughout – more on that later.
Speed
In our tests we see a 35% boost in how fast the pages load with the new templates. This was one of the most important aspects of the redesign and something we will continue to improve on. Sometimes we still see badly behaving ad units that slow things down and while we try to tackle this they appear — it’s often like a game of whack-a-mole, but we’re doing everything we can on our end to make our codebase as quick as possible.
Clarity
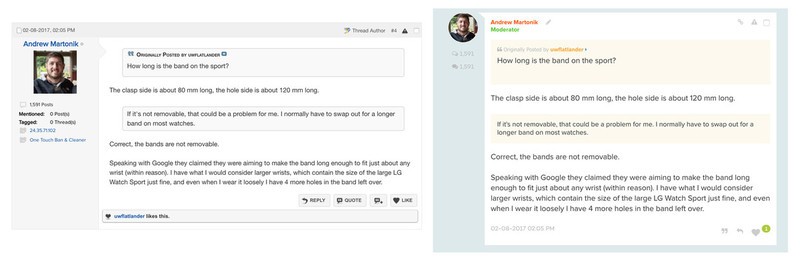
More than 80% of our Forum traffic comes from Google, and to be frank, a user coming into the forums blindly for search wouldn’t have a good experience. We saw issues with how far you had to scroll to see the content you came for and a lack of visual queues telling you this was a conversation.
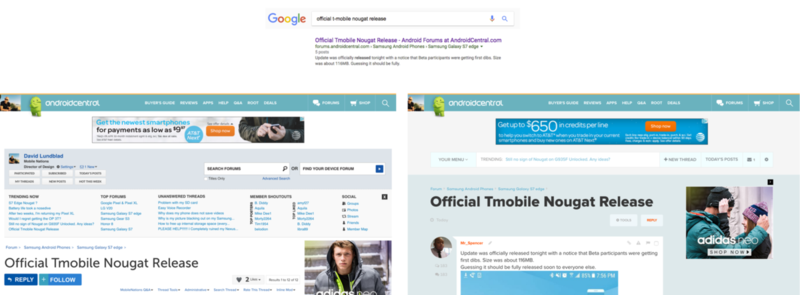
Hierarchy
In the old forums everything had the same ‘weight’ and demanded the same amount of attention. In our new design we have a clear idea about what we want to stand out and what can be in the background. This means that some actions that were previously exposed and very clear to the experienced VB user are now slightly more hidden.
Our priority — what we want a visitor to immediately grasp — is that they are in the right place (Forum Thread Title) and that this is a conversation (Avatar + Post that looks like a message). Everything else can take a back seat.
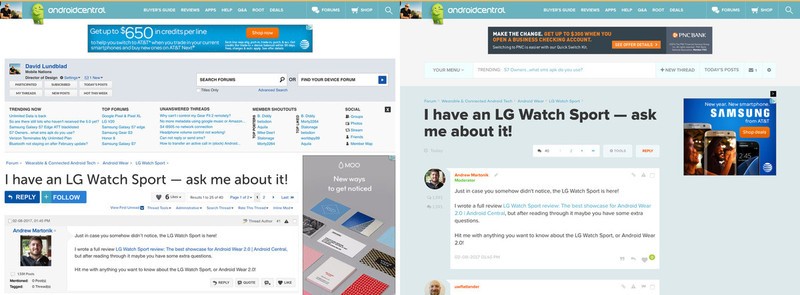
Recognition
Our forums are built off of VBulletin, a long-standing software that underpins many other large and popular communities. The problem is that the base styling, which we also had based our old interface on, was also old and long-standing. The old-school style of forums is no longer the only way that people engage in serious conversations online. The kind of discussions we see in our Forums also happen in Facebook comment threads, Quora, Twitter replies, and a host of other group messaging apps. It made sense for us to at least visually move towards the look and feel of these hugely popular platforms — they’re not just modern, they’re simplified from the masses of forum controls in a very smart way.
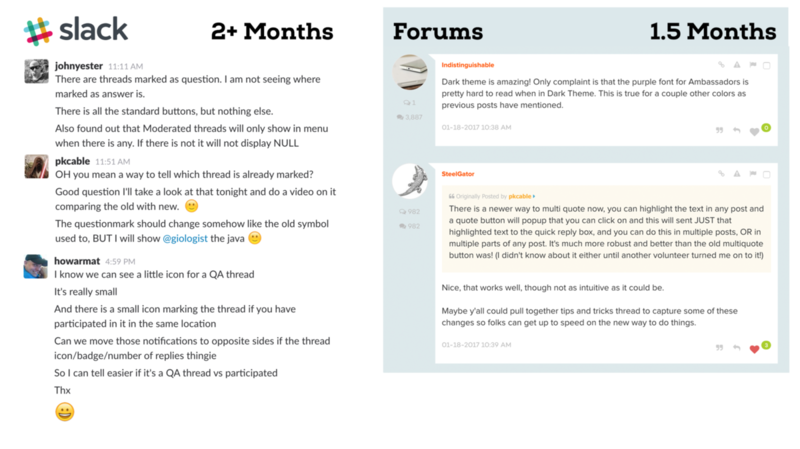
By the Community
This has been the most extensive user testing we’ve ever done and we believe it’s paid off. Since late November 2016 a group of select Forum users have been giving us nonstop feedback through slack — a BIG thank you to all of you! In late December we also opened up access to volunteers who have been helping us out with additional feedback in this forum thread.
I seriously cannot stress enough how important this feedback process has been — it’s the best decision we’ve ever made.
Dark Theme
Sorry it took us so long! Enough said 🙂

You can find the Dark Theme inside Your Menu at the very bottom right – hidden away behind a moon icon like a little Easter egg.
Mobile with all the Trimmings
We wanted you to have all the same tools you enjoy on the desktop while using a mobile phone. This also means our Moderators and Ambassadors have the ability to do their work more easily on the go than before.
Small tweaks and Fixes everywhere
In addition to the huge overall changes we’ve made a bunch of smaller changes throughout the forums. You might not notice them for a while, and many are back-end tools that will make life easier for our volunteer Moderators. It’s been a big project for us and we are really happy with the attention to detail it forced upon us. We are suitably humbled by the complexity of doing any changes to a tool many of you spend hours in every day.
Lastly, we fully expect there to be more issues and for our members to have better ideas than we have on how to improve the Forums. Please engage in the conversation over here in this forum thread — we really want your feedback, good and bad, so that we can continue to improve these forums for you.
Thank you!
Is your Pixel randomly shutting off Bluetooth? You’re not alone
My Pixel’s got the Bluetooth Bug Blues…
The Google Pixel has been a bit buggy after this month’s February update, and Google has identified a fix for one of the more noticeable ones: your Bluetooth randomly shutting itself off. Listed in the Pixel’s Product forum, community leaders say that a fix has been identified and that it will be pushed out in a coming release, hopefully alongside the March security update.

The issue that many Pixel users have experienced is an infrequent but nevertheless annoying disabling of Bluetooth without the user having gone anywhere near the settings. If you’re playing music through a Bluetooth speaker at the time, it’s easy to detect, but for most of us, you don’t find out until your phone keeps dinging for notifications and your wrists doesn’t, or when you get in the car and your tunes never start up.
Numerous users have been chiming up with this issue in the Pixel User Community, helping the Pixel team find the issue and identify a fix. There doesn’t seem to be much of a workaround while we wait for said fix to roll out, but it’s good to know that it’s not just us, and it will be fixed. Hopefully soon.
Google Pixel + Pixel XL
- Google Pixel and Pixel XL review
- Google Pixel XL review: A U.S. perspective
- Google Pixel FAQ: Should you upgrade?
- Pixel + Pixel XL specs
- Understanding Android 7.1 Nougat
- Join the discussion in the forums!
Google Store
Verizon
Verizon takes top spot in latest RootMetrics nationwide report
Another carrier report, another win for Verizon… but the gap is closing
T-Mobile’s been jumping up and down claiming it’s the best network now, pointing to an OpenSignal report in some of its most recent bragging. This week, we have another report from RootMetrics, which claims, as it has claimed for a while now, that Verizon is still top dog nationally in each of their six categories. So, who’s right? Who’s wrong? Who’s best? Who’s worst?
Well, like a lot of statistics and reports, it comes down to the method for collecting the data.

OpenSignal is crowd-sourced, meaning that they pull data from users where they can get them, and since most of the crowd on OpenSignal is in cities (like most of the nation’s populace), T-Mobile gets a better rating and a better report because T-Mobile performs better in metro areas than rural areas. RootMetrics isn’t crowd-sourced, but a more calculated analysis that balances rural and metro demographics more accurately.
So, in cities, T-Mobile has a bit better chance of working well, and if you’re a city-dweller, that’s great news for you. If you’re out in the sticks, those OpenSignal numbers aren’t going to be as accurate to you as the RootMetrics score. RootMetrics still puts Verizon in first place and AT&T as a close second.
Who’s the best? Well, that depends where you are.
Who’s the worst? Sprint.

Cloudbleed: What you need to know and what you need to do

Cloudflare has had a sizeable data leak. Here’s what that means for you.
On February 17, 2017, vulnerability researcher from Google’s Project Zero Tavis Ormandy stumbled across what looked like a really nasty data leak from Cloudflare, a web performance and security company. He quickly contacted the “right” people at Cloudflare and the situation was fixed in less than an hour.
Any data breach can be significant. Especially when a service has over one billion users. We’ll direct you to the Cloudflare incident report for the full details of what happened (warning: it’s pretty technical). In layman’s terms, data was leaked that was potentially sensitive. This data was available to anyone, even web spiders used by search engines. SSL keys were not leaked.
The Cloudflare features that used the affected HTML parser (email obfuscation, Server-side Excludes, and Automatic HTTPS Rewrites) were in use by a lot of companies. Most likely companies that you have online accounts with, This means your data may have been exposed.
Mobile Nations uses some of Cloudflare’s services. In fact, you’ll find us on the list floating around of sites potentially affected. We have verified that the affected services aren’t in use nor have ever been used on any Mobile Nations sites.
After investigation, the features behind #Cloudbleed (Email Obfuscation, SSE, HTTPS Rewrites) have never been active on @MobileNations sites
— Marcus Adolfsson (@madolfsson) February 24, 2017
We also received notice from Cloudflare about the leak and they had this to say:
Your domain is not one of the domains where we have discovered exposed data in any third party caches. The bug has been patched so it is no longer leaking data. However, we continue to work with these caches to review their records and help them purge any exposed data we find. If we discover any data leaked about your domains during this search, we will reach out to you directly and provide you full details of what we have found.
Look for a similar statement from other places you have an account with for information about your data that may have been exposed.
What should I do

Like most big security instances, we’ll never know the full details of what was and wasn’t leaked out. We can confirm that we aren’t using the services that were mentioned as vulnerable, but we don’t know how anything else on Cloudflare’s servers might have been affected. Every Cloudflare customer is in the same boat.
That means it’s time for you to get proactive.
Change the password for all of your online accounts
Yes, this sucks, but know what sucks more? Having someone get your details and have access to stuff you don’t want them to have access to. Use a password manager and let it make crazy passwords and remember them for you if you don’t have your own password management routine. If you haven’t used a password manager in the past but wanted to check one out, now is a perfect time.
More: Best password managers for Android
Now is also a good time to remember that you should be changing your passwords regularly, which makes a password manager a must if you have a lot of accounts.
Enable two-factor authentication on every account that has it available as an option
If you have two-factor authentication enabled, someone else with your login details still won’t be able to access your account. Two-factor authentication can also be a pain in the butt sometimes, but it’s the best way to protect yourself when a big data breach happens, like the one we’re seeing now.
Here are some resources on two-factor authentication.
- What you need to know about two-factor authentication
- How to set up two-factor authentication on your Google account
- Add a USB Security Key to your Google account
- Wireless security keys now work on Android
- Download Google Authenticator
- List of websites and whether or not they support 2FA.
Nothing we can do will prevent these kinds of data leaks. The important thing is what we can do to protect ourselves when they happen,




